Resolv Attack: The Survival Logic Paradox of Yield-Bearing Stablecoins
- Core Viewpoint: The hacker attack on Resolv Labs exposed deep-seated vulnerabilities in the yield-bearing stablecoin sector regarding risk management, infrastructure security, and systemic trust assumptions. The root cause lies in the excessive pursuit of capital efficiency at the expense of safety redundancy, revealing the layered contagion risks within DeFi Lego combinations.
- Key Elements:
- The attacker gained privileged private keys by compromising Resolv's AWS KMS cloud environment and exploited a critical vulnerability—the contract's lack of on-chain verification—to mint 80 million unbacked USR stablecoins out of thin air using only about $200,000 in collateral.
- The attacker cashed out approximately $24 million by selling on DEXs, causing the USR price to plummet 97.5% within 17 minutes, triggering the depletion of Curve liquidity pools and large-scale forced liquidations on lending protocols like Morpho.
- The incident triggered systemic contagion. Morpho protocol's "Public Allocator" function, which relies on risk-free automated scripts, continued injecting funds into the already depegged market post-attack, resulting in approximately $6 million in losses.
- Resolv employed a Delta-neutral strategy pursuing 1:1 capital efficiency, and its risk absorption layer (RLP) was held by institutions seeking high yields. The system lacked a buffer, ultimately leaving RLP holders and others to bear the majority of the losses.
- This event serves as a warning that DeFi security must go beyond code audits, adhere to the "zero trust" principle, and strengthen private key management, real-time monitoring, and risk isolation to address external dependencies and infrastructure risks.
Original Author: @BlazingKevin_, Blockbooster Researcher
On March 22, 2026, Resolv Labs, a DeFi protocol based on a Delta-neutral strategy, suffered a severe hack. The attacker exploited a critical vulnerability in the minting mechanism of its stablecoin, USR, using only approximately $100,000 to $200,000 worth of USDC as collateral to mint 80 million unbacked USR out of thin air. Subsequently, the attacker sold the tokens on DEXs through a sophisticated money laundering path, cashing out approximately $25 million. This caused the price of USR to plummet to $0.025 within just 17 minutes, a staggering drop of 97.5%. This incident is not merely a simple code vulnerability; it reflects the deeper fragility of the "yield-bearing stablecoin" sector in terms of risk management, infrastructure security (especially private key and cloud environment management), and systemic trust assumptions.
Based on an in-depth reconstruction of the Resolv Labs attack, this article expands its perspective to the macro-history of yield-bearing stablecoins, deconstructing the chain collapse of USDX/xUSD/deUSD in November 2025, as well as the severe damage to the "Curator" ecosystem of lending protocols, the systemic failure of risk-free automated scripts under extreme market conditions, and the layered contagion risks within the DeFi Lego bricks in this event.
1. Background: Resolv Labs' Frenzy and the Hidden Dangers of a Two-Layer Risk Architecture
1.1 The Irrational Exuberance of Resolv Labs Fueled by Capital
Resolv Labs was incubated by the well-known crypto research institution Delphi Labs. In April 2025, Resolv Labs announced the completion of a $10 million seed round led by Cyber.Fund and Maven11, with participation from industry giants such as Coinbase Ventures and Animoca Brands. This prestigious investor lineup provided Resolv with strong trust endorsement, giving it a significant advantage in early-stage liquidity acquisition.
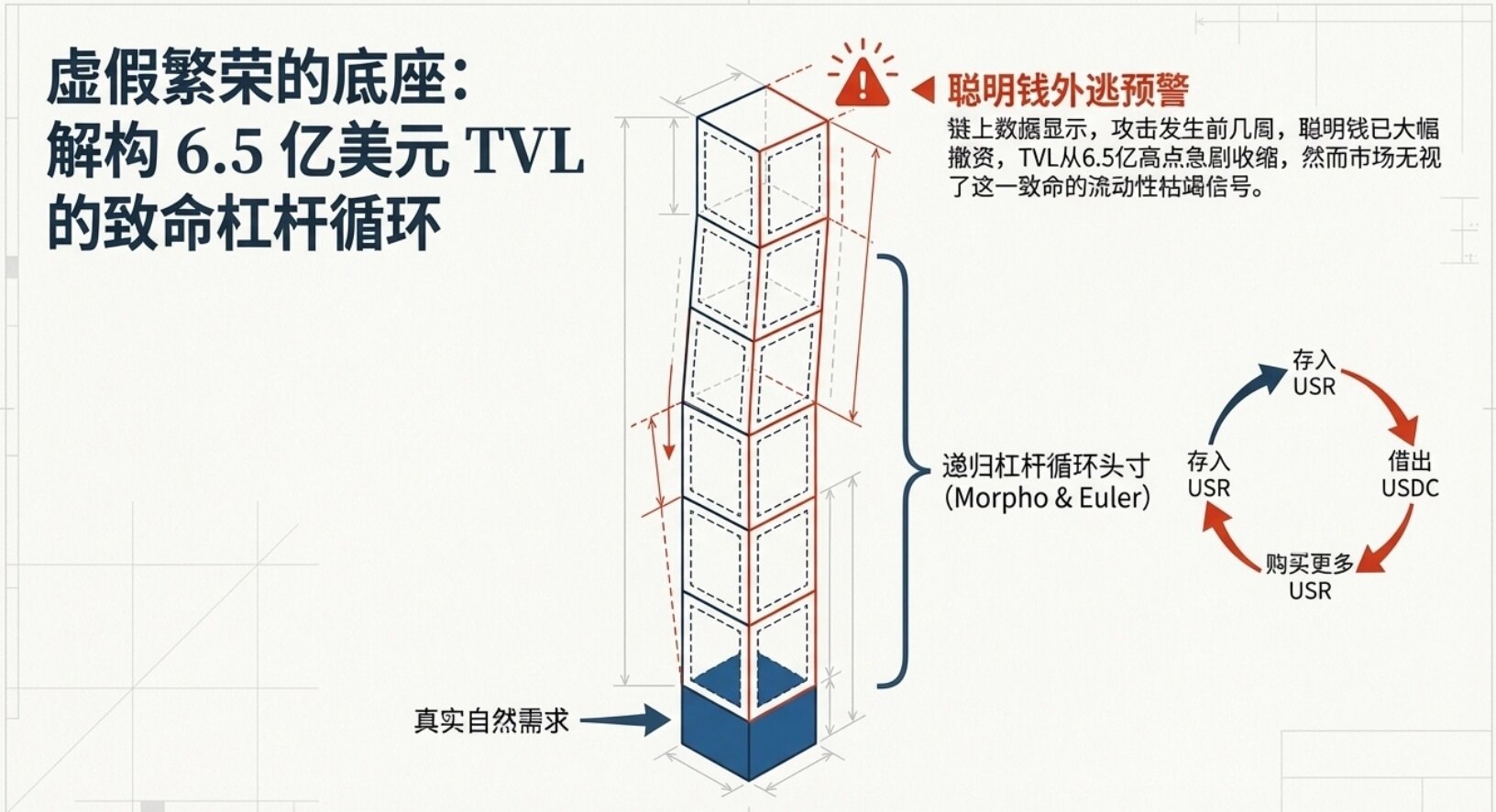
Prior to the attack, its TVL exhibited exponential, explosive growth, soaring from less than $50 million to a peak of over $650 million in less than three months. However, this prosperity was not built on genuine organic demand but was primarily driven by leveraged loop strategies on lending protocols like Morpho and Euler. Users deposited USR into lending protocols, borrowed USDC, and purchased more USR, repeating this cycle to amplify returns. This "left foot stepping on the right foot" false prosperity greatly amplified the system's fragility.
Furthermore, Resolv's superficial efforts in security were not lacking. It had undergone 14 or even 18 audits by 5 renowned security firms, partnered with Immunefi to establish a $500,000 bug bounty program, and deployed Hypernative's real-time threat monitoring system. However, when the attack actually occurred, these costly traditional security measures proved utterly ineffective, prompting industry reflection on the current DeFi audit model.
1.2 The Inherent Contradiction of the USR Stablecoin and Delta-Neutral Strategy
Resolv's core product is USR (Resolv USD), a yield-bearing stablecoin backed 1:1 by on-chain assets. To achieve high capital efficiency, Resolv abandoned the traditional over-collateralization model in favor of a complex Delta-neutral strategy.
Specifically, when users deposit stablecoins like USDC, Resolv converts them into ETH or BTC and deposits them into yield-generating venues. Simultaneously, to hedge against spot price volatility risk, Resolv opens equivalent perpetual contract short positions on partnered centralized or decentralized exchanges. This "spot long + contract short" combination, in theory, keeps the portfolio's net value pegged 1:1 to the US dollar (i.e., Delta = 0), while earning staking yields and funding rates from the contract market. In bull markets, funding rates are typically positive, allowing USR holders to achieve annualized yields of approximately 5-6% or even higher.
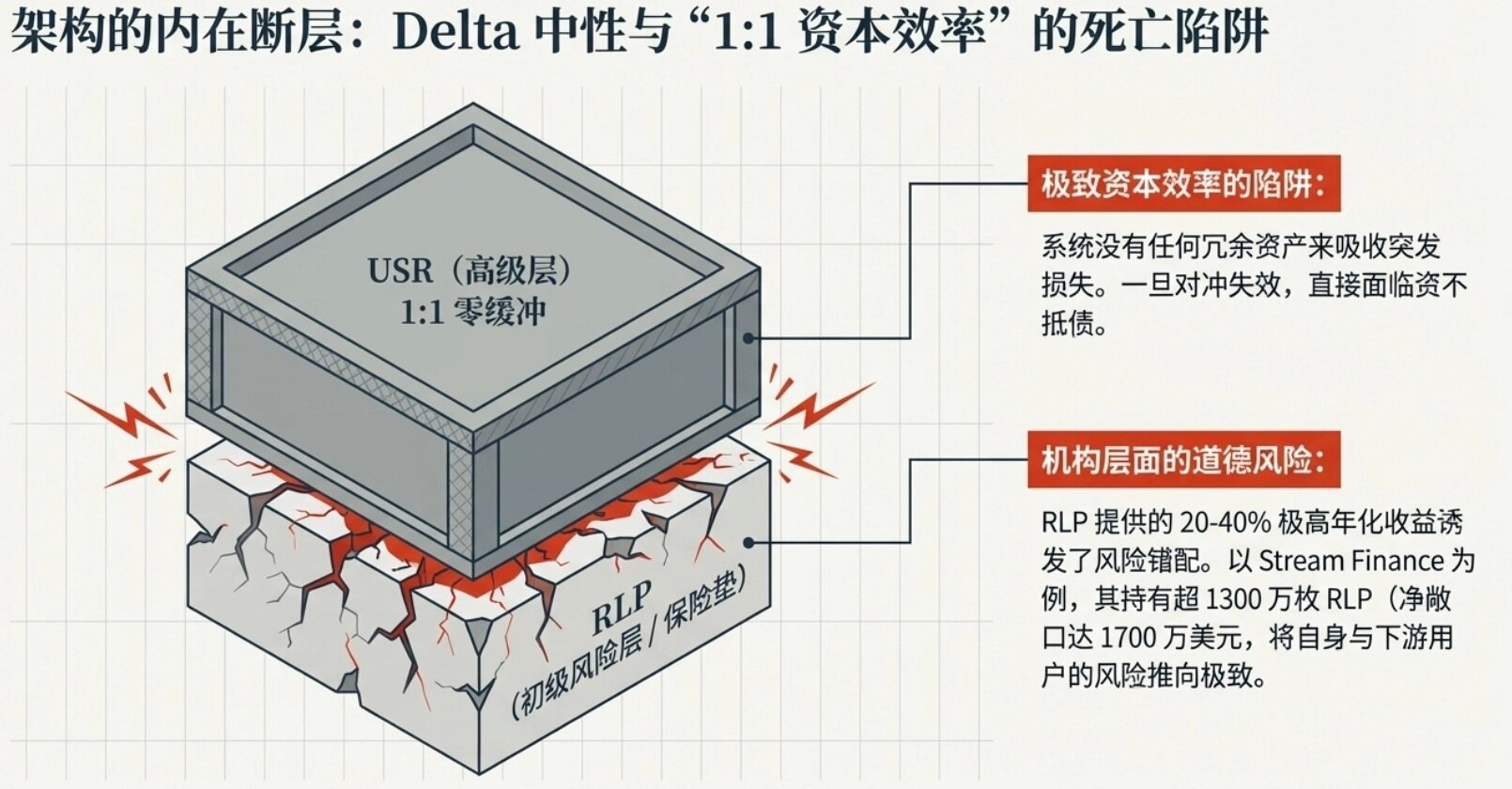
However, the inherent contradiction in this design lies in its deep binding of crypto-native decentralized assets with the derivatives markets of centralized exchanges, introducing complex counterparty and operational risks. The "1:1 capital efficiency" means the system has no buffer; once the hedging mechanism fails, the system faces immediate insolvency.
1.3 RLP: The "Insurance" Layer for Risk Absorption and Moral Hazard
To address the potential tail risks of the Delta-neutral strategy (such as prolonged negative funding rates causing continuous protocol losses, or exchange Auto-Deleveraging events), Resolv designed a two-layer token architecture. In addition to the senior layer USR, the protocol introduced the RLP token as the junior risk layer.
RLP represents the "excess" portion of the collateral pool beyond the 1:1 ratio, acting as the insurance layer for the entire protocol. When the system incurs losses, the net value of RLP is written down first to protect the principal of USR holders. As compensation for bearing high risk, RLP holders receive the majority of the protocol's residual yield, with annualized returns reaching 20-40% at their peak.
Before the incident, the total circulating supply of RLP was 30 million tokens, valued at approximately $38.6 million. The largest holder, Stream Finance, held about 13.6 million RLP, representing a net risk exposure of roughly $17 million. While this design seems financially logical, in practice, it triggered severe moral hazard: lured by high yields, a significant amount of institutional capital pursuing high returns flooded into RLP, and these institutions often passed the risk downstream to retail investors. When a crisis erupts, the so-called "insurance layer" itself is often already fragile.
2. Attack Technical Reconstruction: Cloud Infrastructure Compromise and the Collapse of Zero-Trust
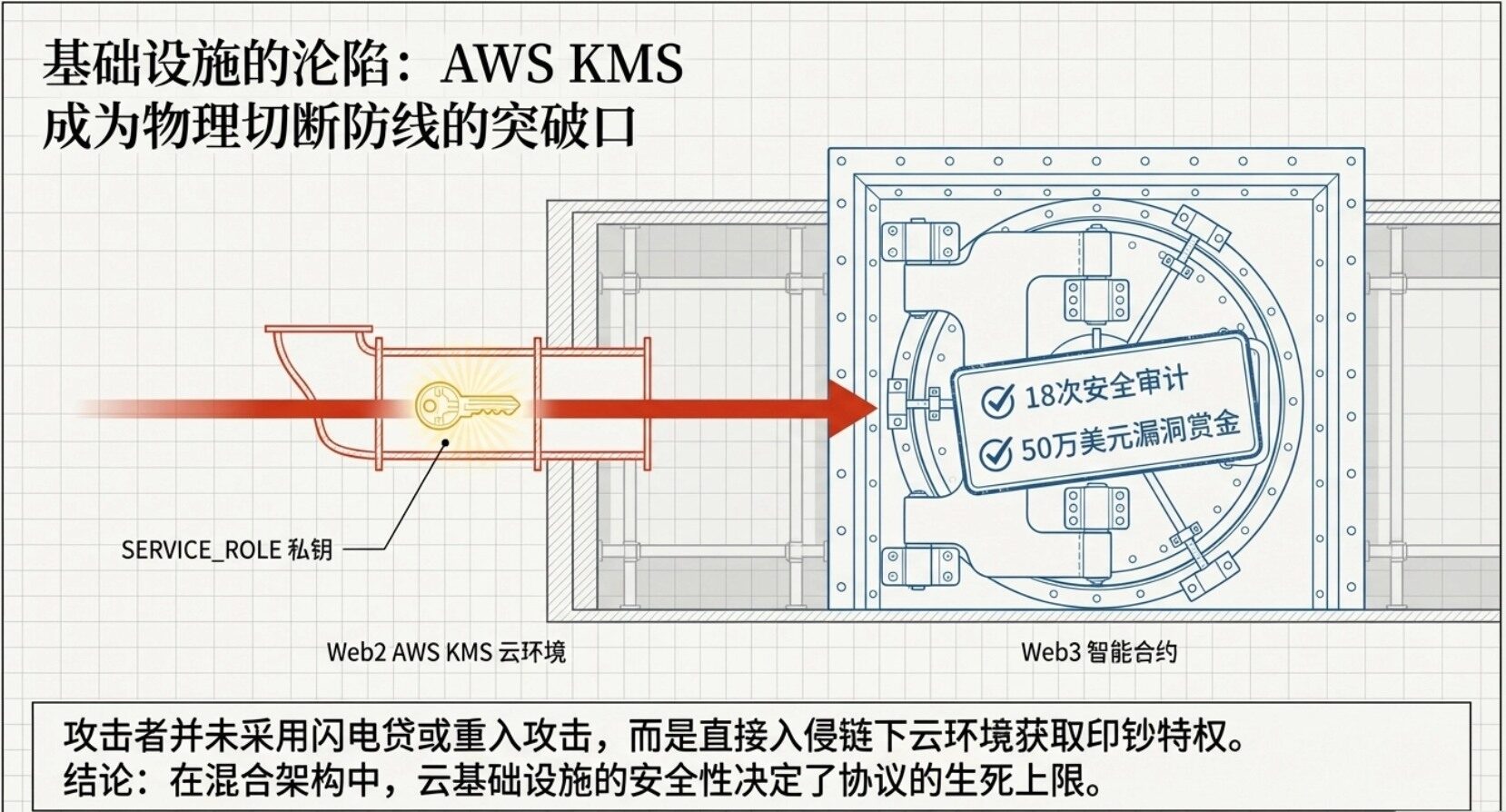
This incident was not merely a smart contract breach but a case of Web2 cloud infrastructure vulnerabilities spreading to Web3. The attacker launched what is known as a "500x leverage" unbacked minting attack, completely breaching Resolv's defenses.
2.1 Attack Vector: The Compromise of the AWS KMS Cloud Environment
In the early stages of the incident, the community widely speculated that a smart contract logic flaw or oracle manipulation caused the attack. However, according to subsequent on-chain security tracing by Chainalysis and deep analysis of infrastructure vulnerabilities.
The attacker did not use common DeFi attack vectors like flash loans or reentrancy but directly targeted Resolv's off-chain cloud infrastructure. The attacker, through some means (possibly phishing, insider leaks, or cloud service misconfiguration), successfully breached Resolv's Key Management Service environment hosted on Amazon Web Services.
This environment stored the protocol's crucial privileged signing private key (SERVICE_ROLE). This private key is responsible for verifying user deposits off-chain and sending final minting instructions to the on-chain contract. By gaining control of the KMS environment, the attacker essentially gained control of Resolv's "money printing press," allowing them to bypass all front-end restrictions and directly issue legitimate minting commands to the smart contract.
2.2 The Fatal Flaw: Missing On-Chain Verification and Single Point of Failure
Even if the attacker obtained the private key, losses could have been limited to a minimal range if the smart contract was well-designed. However, Resolv's design flaws at the smart contract level magnified this crisis countless times.
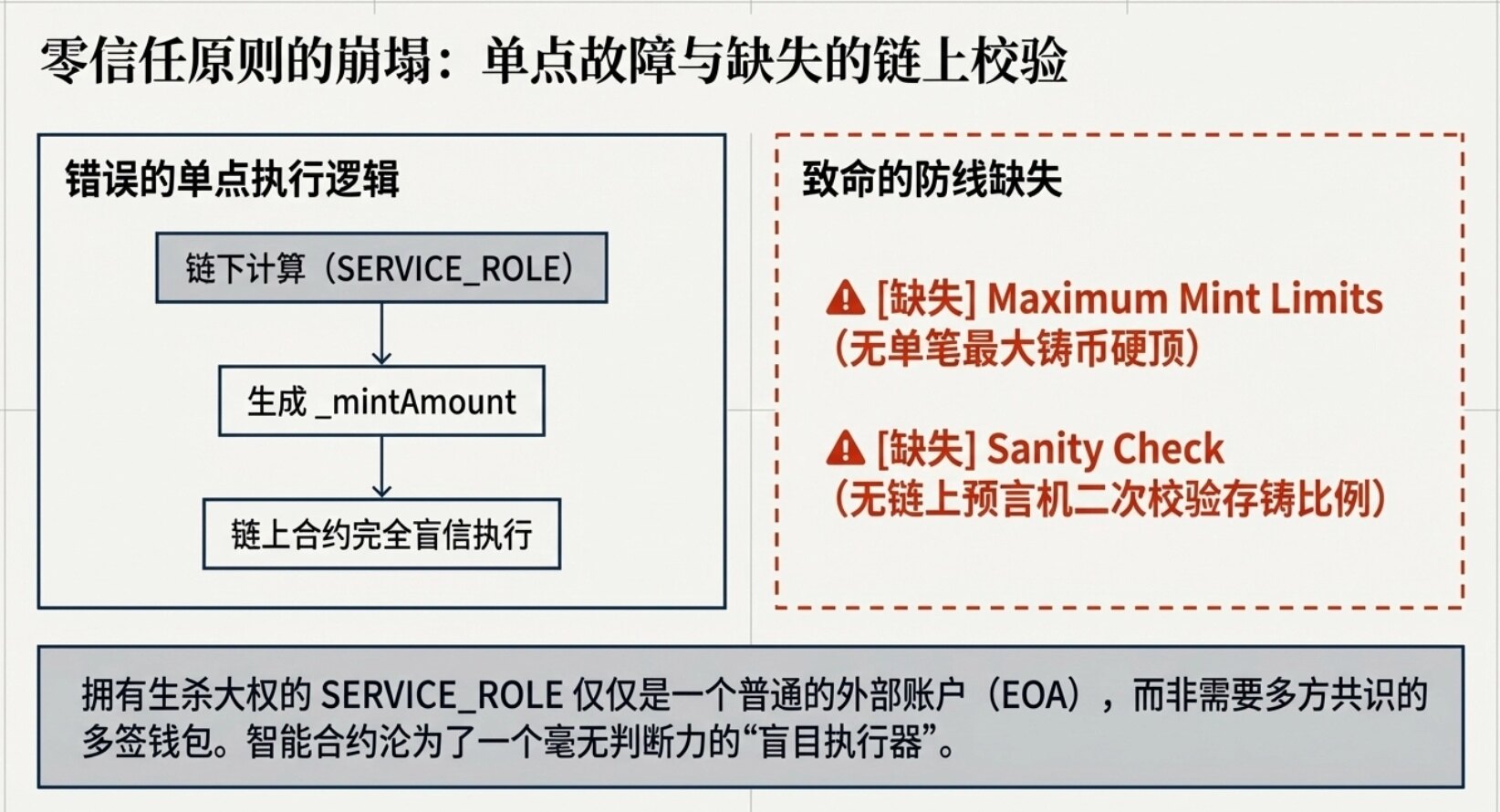
Resolv's USR minting process consisted of two steps:
1. Request Phase: The user initiates a request on-chain (requestMint or requestSwap), depositing USDC into the protocol's vault.
2. Execution Phase: The project's off-chain backend service (with SERVICE_ROLE permissions) monitors the request, uses the Pyth oracle off-chain to check the value of the deposited assets, calculates the amount of USR to mint, and then calls the on-chain contract's completeMint or completeSwap function, passing the _mintAmount parameter to complete the minting.
The core issue was that the minting contract blindly trusted the _mintAmount parameter provided by the SERVICE_ROLE. The contract code neither set a hard cap on the maximum mint amount per transaction nor performed an on-chain sanity check via an oracle to verify the ratio between the deposited amount and the minted amount.
This design severely violates the core philosophy of DeFi—the "zero-trust" principle. Worse still, this all-powerful SERVICE_ROLE was merely a regular Externally Owned Account (EOA), not a multi-signature wallet (Multi-Sig Wallet) requiring multi-party consensus. Once this single private key was compromised, the attacker could arbitrarily manipulate the mint amount.
2.3 Attack Execution and Disastrous Emergency Response
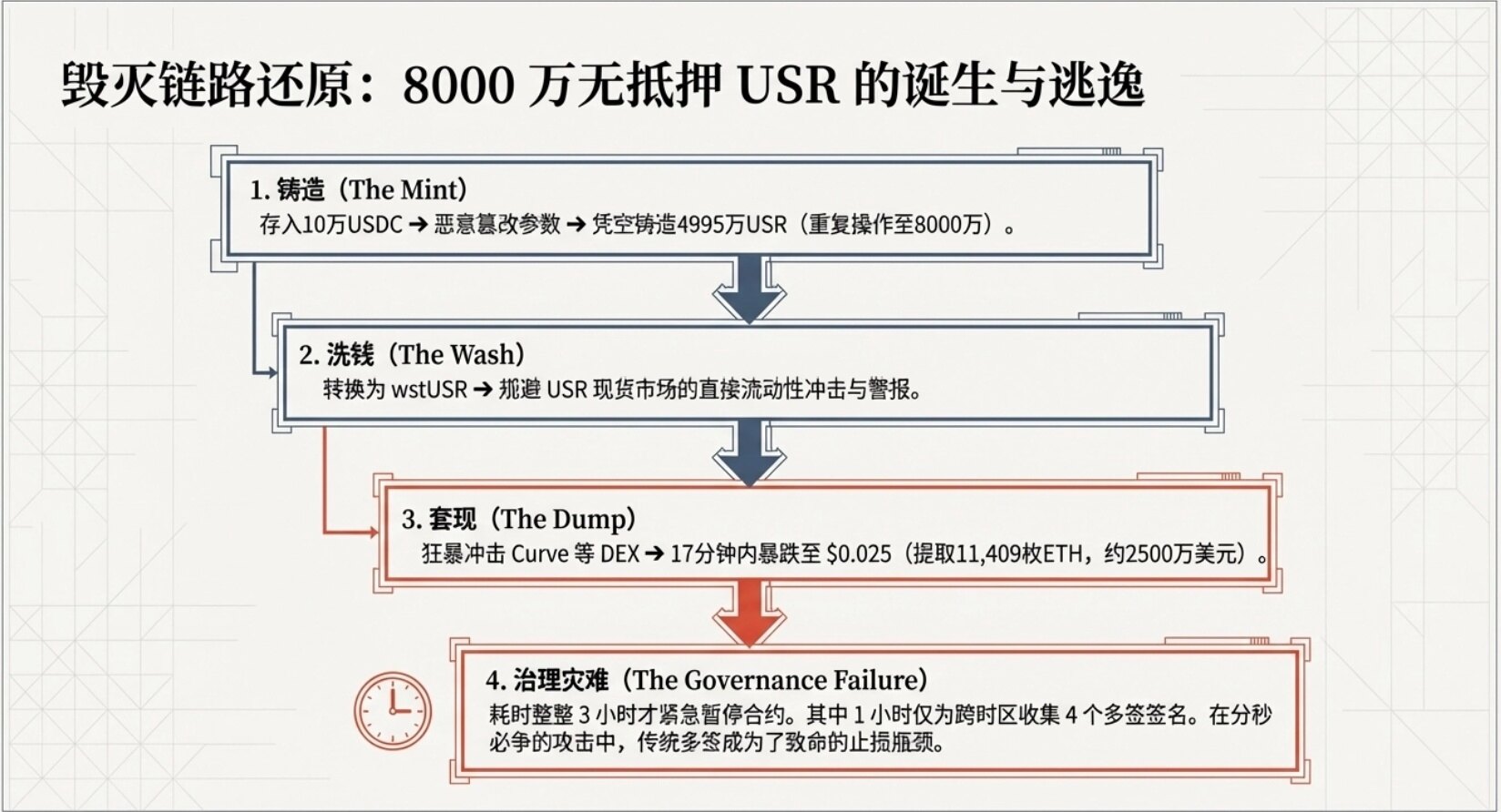
After gaining "minting authority," the attacker acted swiftly and decisively:
1. Small Deposit and Infinite Amplification: Around 10:21 Beijing Time on March 22, the attacker first made a normal on-chain request, depositing approximately 100,000 USDC. Subsequently, they used the compromised SERVICE_ROLE private key to call the completion function, maliciously altering the intended mint amount of 100,000 to 49.95 million. Nearly 50 million unbacked USR were instantly created out of thin air.
2. Repeated Harvesting: After confirming the success of the first attack, the attacker repeated the process, depositing another 100,000 USDC and minting an additional 30 million USR. At this point, the attacker, with a cost of only about $200,000, had created 80 million USR with no asset backing.
3. Fund Flow, Market Crash, and the Systemic Collapse of the Ecosystem
3.1 Sophisticated Cash-Out Path
After obtaining 80 million USR, the attacker first converted a large amount of USR into wstUSR (Wrapped Staked USR). wstUSR is a staking derivative token whose value represents a share in the staking pool, not a fixed 1:1 peg to USR. Through this intermediate step, the attacker successfully circumvented the liquidity constraints of directly impacting the USR spot market, transferring the massive selling pressure to the less liquid but more fungible and concealable derivative market.
Subsequently, the attacker used various DEXs and cross-chain bridges to batch and frequently exchange USR and wstUSR for USDC and USDT, ultimately converting all proceeds into Ethereum (ETH).
The immense selling pressure instantly drained the liquidity of the Curve USR/USDC pool. Within just 17 minutes, the price of USR plummeted from $1 to $0.025. Although the attacker ultimately only successfully cashed out approximately 11,408 ETH (worth about $24 million), with an actual cash-out rate of only about 30% (the remaining 70% of value evaporated due to massive slippage from liquidity depletion), this $24 million in real capital outflow was enough to deal a devastating blow to the Resolv protocol.
The Fatal Backlash of Multi-Sig Governance: During the crisis, Resolv Labs' emergency response was disastrous. After the hacker completed the first attack, the protocol took a full 3 hours to be urgently paused. Approximately 1 hour of this delay was solely for collecting the 4 signatures required for the multi-signature transaction. This cross-timezone, multi-entity multi-signature mechanism, a safeguard for decentralization and preventing internal malfeasance in peacetime, became a fatal bottleneck hindering rapid loss mitigation when facing a hacker's time-critical draining attack.
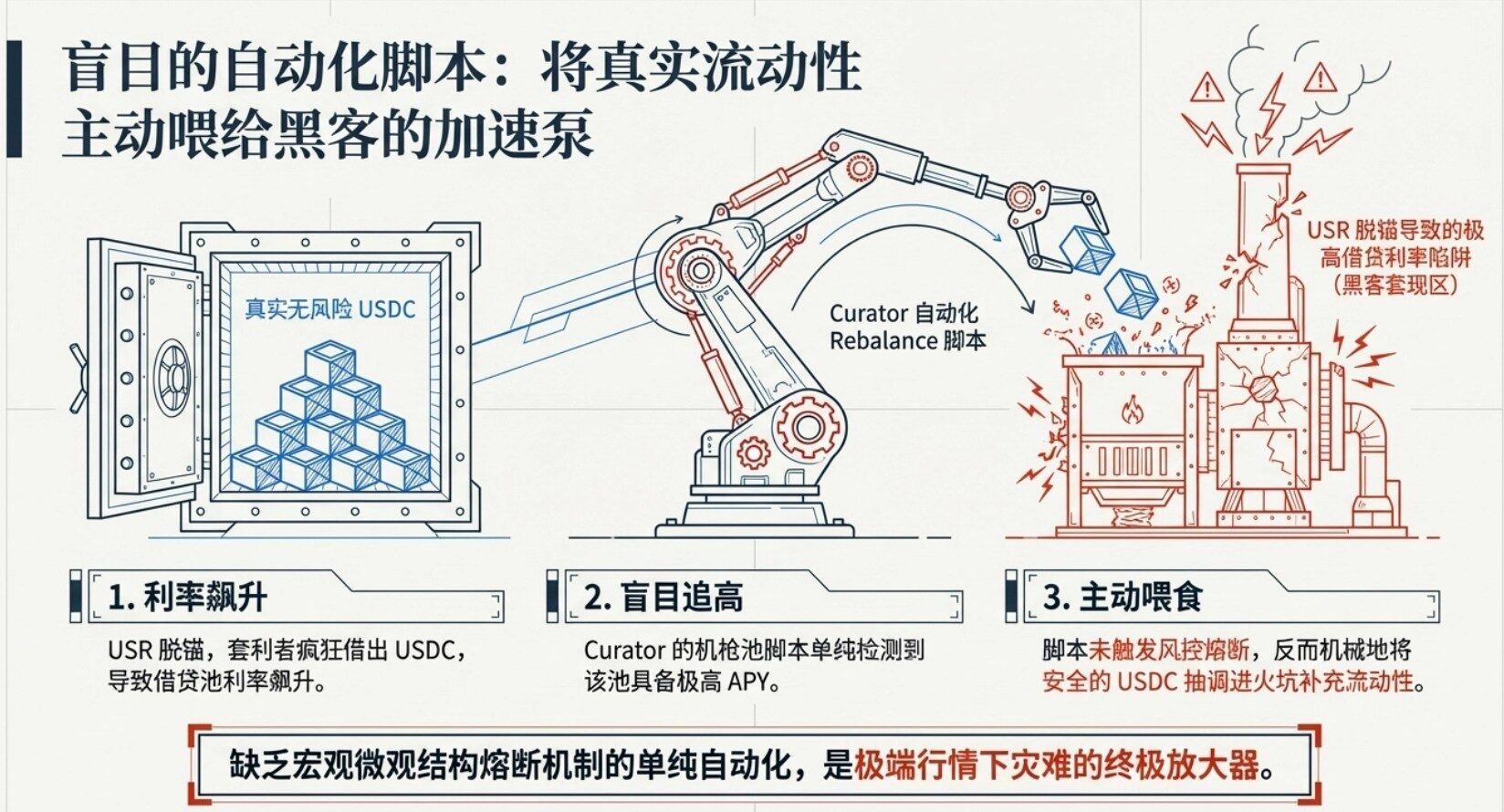
3.2 Morpho and Public Allocator: The Backlash of Risk-Free Automation
The USR de-peg event triggered strong ripple effects, with one of the most notable victims being the Curator ecosystem on the Morpho lending protocol. Morpho officially disclosed that among the 500 vaults with deposits exceeding $10,000, approximately 15 had significant exposure to the affected market.
The Core Amplifier of the Disaster: Public Allocator
Morpho has a feature called "Public Allocator." Its original design purpose is to monitor the utilization rates of various lending markets. When a market's yield spikes, it automatically allocates USDC from vaults to capture higher yields for curators. In normal markets, this is an elegant capital efficiency tool.
However, after the attack, arbitrageurs bought USR at a discount after the de-peg and deposited it as collateral into the protocol. Since the protocol's internal oracle still priced it at $1, arbitrageurs used this price difference to borrow real USDC, causing the USR market utilization to instantly skyrocket. At this point, automated vaults from institutions like Gauntlet detected the "high-yield signal" but were unaware it was a "trap" market, leading them to continuously inject funds:
- Gauntlet initiated automatic allocation about 20 minutes after the attack began, lasting approximately 90 minutes.
- Another curator, 9summits, even continued supplying funds for up to 10 hours after the attack until manually discovered and stopped.
- Multiple curators, including Gauntlet, re7, kpk, and 9summits, automatically supplied funds to the Resolv market after the incident.
Ultimately, approximately $6.2 million USDC was provided as "exit liquidity," "fed" to USR borrowers, with 96% of the funds (about $6 million) coming from vaults managed by Gauntlet.
Two Fatal Points:
1. Hardcoded Oracles: These Morpho markets used hardcoded oracles that could not promptly reflect that the asset had become worthless or severely devalued during extreme de-peg events.
2. Risk Management Failure: The role of curators or risk managers should involve human judgment under stress tests, but in this event, they reacted slowly, relying entirely on risk-free automated scripts.
3.3 Who Bears the Losses?
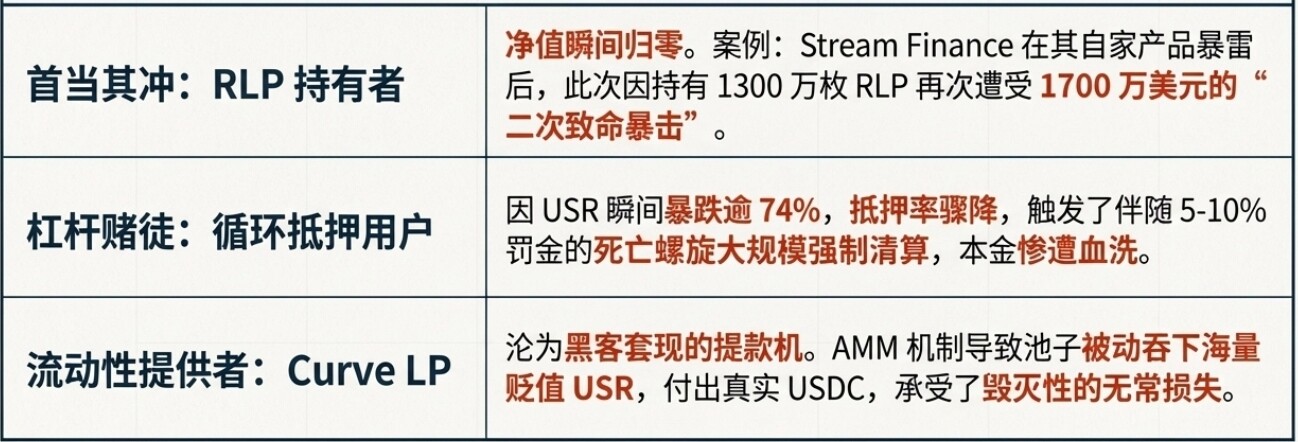
According to Resolv's two-layer architecture and DeFi market logic, the $80 million disaster will ultimately be borne by the following parties:
1. RLP Holders (First in Line): The $80 million in unbacked USR created systemic bad debt, directly causing the net value of RLP to plummet or even go to zero. The most tragic case is Stream Finance. This institution had just been severely hit in November 2025 due to the collapse of its own xUSD, and this time suffered a devastating "second blow" by holding 13.6 million RLP (approximately $17 million exposure). Notably, Stream Finance's official Twitter account has shown no updates since November 2025.
2. USR Leveraged Loop Position Holders: Users who used USR as collateral to borrow USDC on protocols like Morpho and Euler saw their collateral ratios plummet as the USR price dropped over 74% in an extremely short time, triggering massive forced liquidations. These liquidations typically come with 5-10% liquidation penalties, creating classic death spiral pressure and causing significant losses for these users.
3. Curve LP Providers (Liquidity Providers): During the USR crash, the AMM mechanism caused the Curve USR/USDC pool to passively absorb large amounts of devalued USR, paying out real USDC. These LPs suffered immense impermanent loss, becoming the direct ATM for the attacker's cash-out.
4. The Pathology of Yield-Bearing Stablecoin Failures: Structural Root Cause Analysis
Looking back at the history of cryptocurrency, projects attempting to provide native yield or detach from traditional fiat reserves have emerged endlessly, but the vast majority have ended in spectacular failure. These failures are not accidental black swan events but the inevitable eruption of inherent fragility in mechanism design under extreme stress.
4.1 Recursive Leverage and Liquidity Depletion
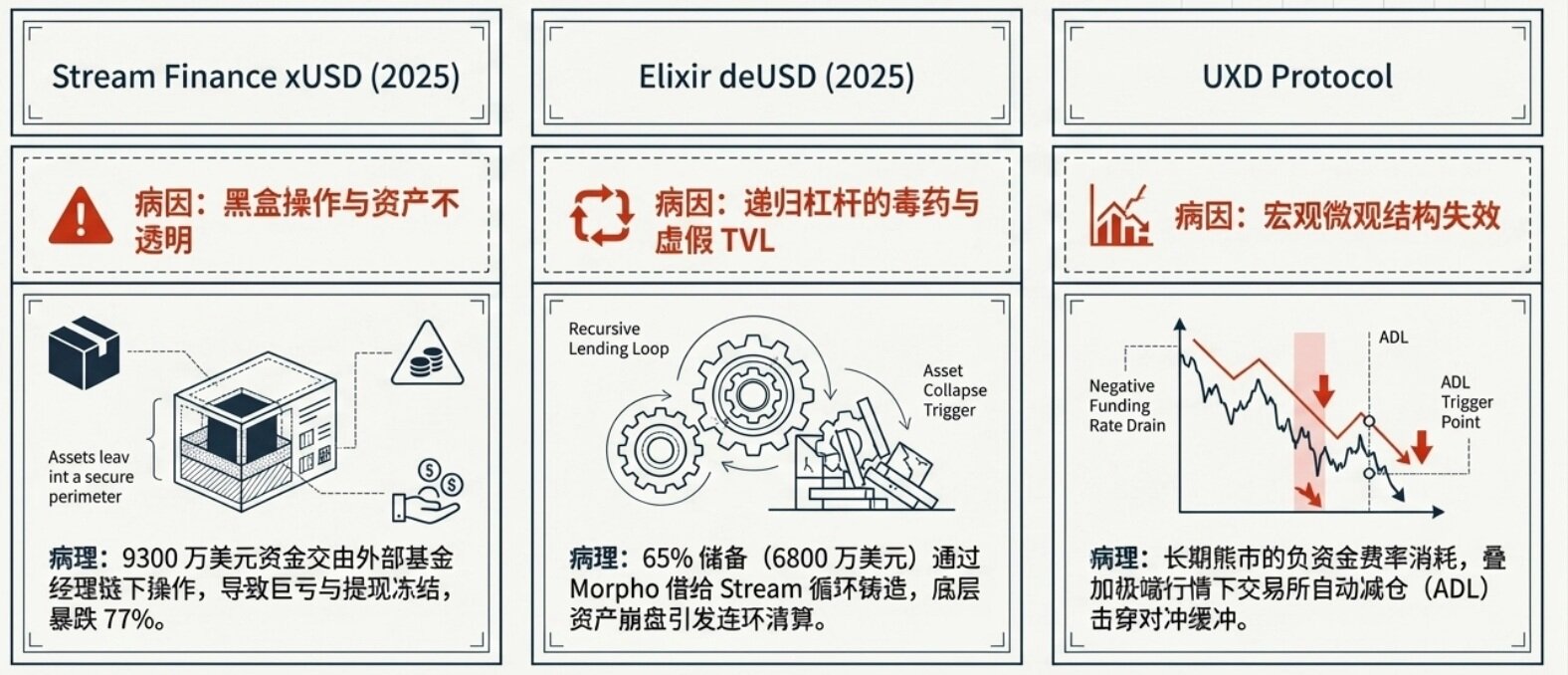
Entering 2025, with the popularity of the "Curator Model" in lending protocols, the risk profile of yield-bearing stablecoins evolved from single-point collapse to systemic contagion. The chain collapse of Stream Finance (xUSD), Stable Labs (USDX), and Elixir Network (deUSD) in November 2025 is a typical representation of this model.
Black Box Operations and Asset Opacity: Stream Finance entrusted a massive $93 million to external fund managers for off-chain operations. This severe black-box operation ultimately led to huge losses and withdrawal freezes, causing xUSD to instantly crash by 77%.
The Poison of Recursive Leverage: Elixir (deUSD), through the Morpho protocol, lent 65% of its reserves (a staggering $68 million) to Stream, with the collateral being Stream's own issued xUSD



